Add layers to create depth of security
Hackers are used to encountering some form of security within an app’s architecture. But often these are thin, disjointed layers of protection that they can easily break through one after the other. That’s why your app security should consist of one thick, connected layer instead.
This depth of security is vital these days. Not least because bad actors tend to use dynamic analysis as their go-to attack method.
Why it matters
- Hackers will quickly think twice about attacking your app when they see how sturdy its defences are. It simply wouldn’t be worth their time or effort to break the interconnected layers.
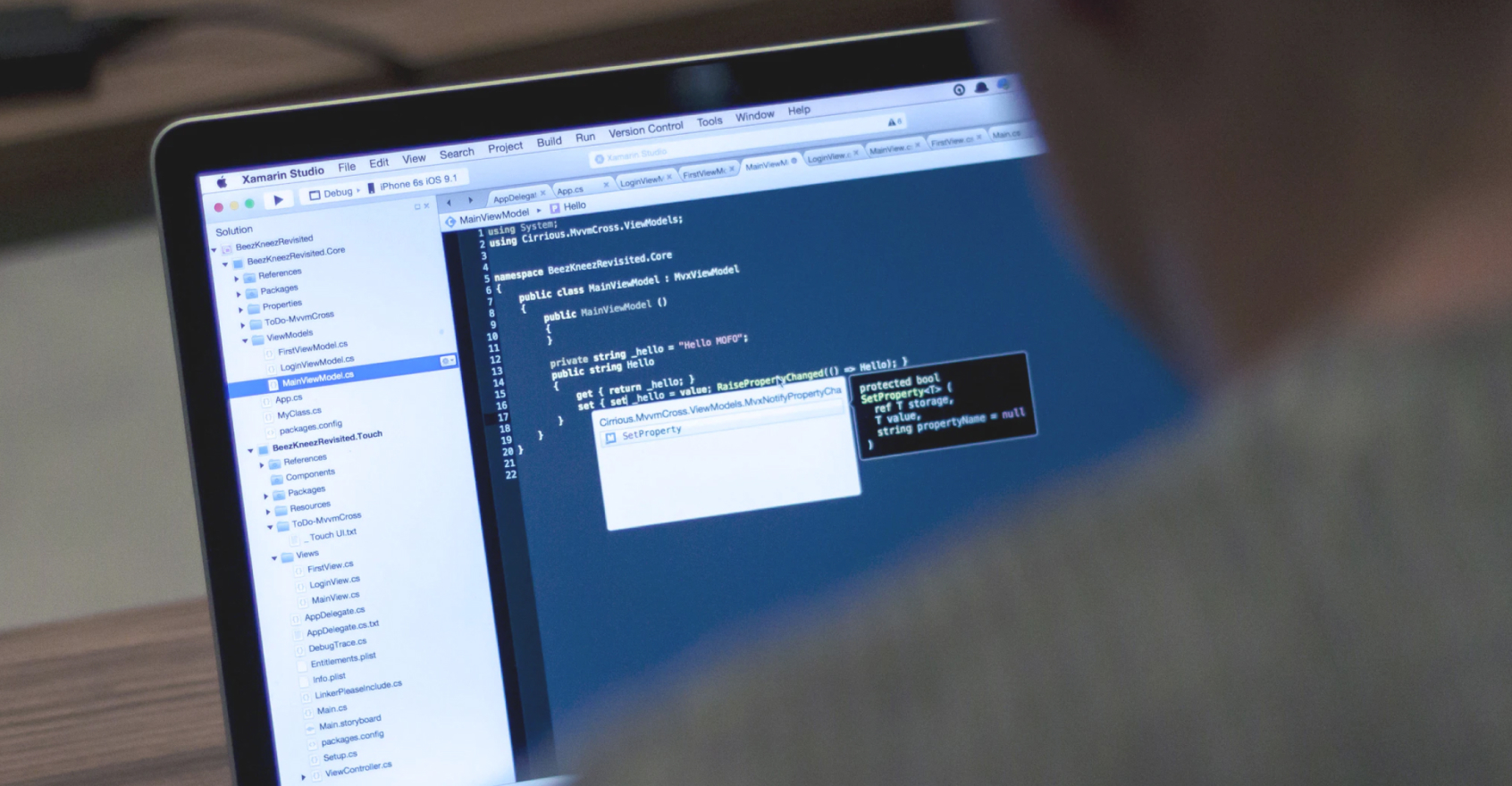
- This approach to designing your security helps to prevent dynamic analysis, too. That’s when hackers use specific tools to analyse the logic of your app.
- It also makes it more difficult for malware to work the way it’s designed to, because it can no longer intercept method calls within the app to steal valuable information.
What you can do
Build a chain of trust
We call this interconnected depth of security the chain of trust. It’s an infinite loop of security that acts as one steel barrier rather than a thousand individual paper ones.
Think about where and how you store cryptographic keys
Utilize platform-specific functionality which is designed for storing sensitive key material. You could also consider using additional security measures like in-app protection and RASP solutions.
Remember that name obfuscation isn’t enough
Some developers still think that renaming functions and variables can keep their app safe from attacks. But name obfuscation isn’t security. Consider it more of an optimization measure.