Fast-tracked trends
Sometimes a trend can be accelerated by a major global event. Think of it like an apple rolling gently down a hillside until it’s given a kick.
Well, the coronavirus pandemic has given several of these apples an almighty boot.
When we look back at 2020 in years to come, our thoughts will naturally be dominated by covid-19. But as we glance through the window into this strangest of years, we’ll see other stories that played out as a side effect of the virus.
We’ll spy the end of the traditional 9 til 5 and long commutes to the office. We’ll hear the death knell for cash ringing out. We’ll witness the rise of the mobile, agile business. And we’ll see the phone cementing its place as our go-to device for, well, pretty much everything.
Cash, of course, was already falling out of favor before we all became much more conscious of cleanliness.
Likewise, businesses were becoming more agile and less static before we all stopped travelling into the center of towns and cities so often.
The apples were rolling. But then came the kick.
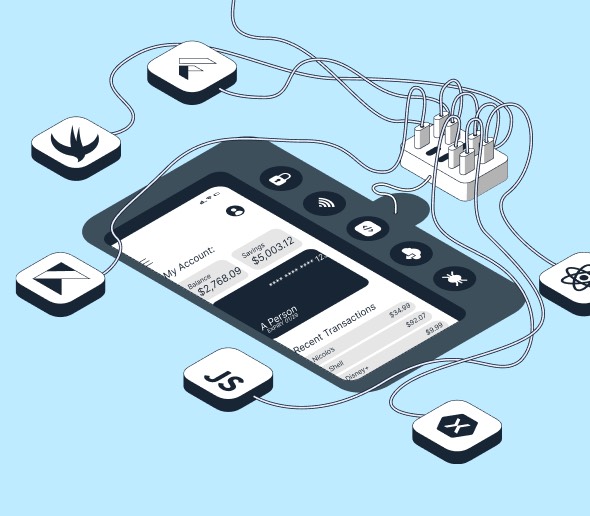
And there’s something that links these last two trends in particular - that is the emergence of SoftPOS (software-based point of sale) technology. This turns the phone into a mobile checkout that companies can take with them as they travel to their customers.
It’s a great solution for them and for their customers, who get a simple way to pay while not having to worry about handling cash.
But wait, we hear you cry. What about security?
Is it really safe for us all to just wander around tapping our phones against others to make and receive payments?
Well, yes. It is. But only if you follow certain guidelines and requirements there to protect the apps that make these instant transfers possible.
Read on and we’ll explain how to protect SoftPOS apps.
The end of the static business
There are two sides to this new payment story. On the one hand, you have the ability to make payments with your phone via a mobile wallet. And then there’s the more recent trend of being able to accept payments via a SoftPOS app on your phone.
Mobile wallets such as Apple Pay and Google Pay have been embraced widely across the globe. Particularly by younger millennial and gen z consumers who have grown up viewing the phone as a payment tool as much as a mode of communication.
But mobile wallet payments look set to gain traction across generations - not just among younger consumers. That’s because they offer convenience and speed alongside associated hygiene benefits that weren’t quite as important before covid-19. After all, NFC technology means you don’t even have to tap your phone against a card reader. It just has to be close to it.
A recent VISA survey highlighted just how much expectations have changed in 2020. Almost half of the consumers polled said that they wouldn’t visit a store where the default payment method involved handling cash or touching a card reader others had used.
Fortunately for those people, more and more vendors are accepting mobile wallet payments. And the contactless limit has been raised during the pandemic to cater to these changing desires.
So, that’s how buying has changed in recent months. But what about the other side of this story?
Well, the vendors that already accept mobile wallet and chip and pin card payments have typically needed to invest in a dongle to do so. And this dongle has to be paired with a mobile device and needs to be charged intermittently.
SoftPOS technology renders this dongle obsolete.
Its arrival is pretty well timed given that businesses aren’t as static as they used to be. The days of companies only waiting for their customers to come and buy something from them are over.
We live in a much more fluid world these days. A world of pop up stores and home deliveries.
A couple of months ago, the Financial Times reported on the demise of Pret A Manger during the covid-19 pandemic. The UK-based sandwich shop is ubiquitous on the high street - particularly in London. Indeed, Londoners often joke that every other store in the capital is a Pret. But as people have stopped commuting to their office in the center of town, Pret’s sales have sunk.
At the end of the Financial Times piece there's a suggestion that might have sounded crazy a few years ago but now somehow seems less outlandish. Namely that Pret could invest in a fleet of vans to drive out of the city center to where their customers live. Then they could play a tune to attract people out of their home office for a coffee or a sandwich.
In this hypothetical scenario, being able to take payments via a mobile device would speed up the process considerably. In difficult times for all businesses - both large and small - the ability to take payments directly via a smartphone could boost flexibility.
SoftPOS could help businesses in remote areas, too. It might be used at pop-up stores and market stalls. And it could be used to take payments on the spot, anywhere in the store.
That would cut down on waiting times, which is quite an attractive prospect for the modern customer used to instant gratification.
For a long time businesses have been guilty of seeing the payment process as an admin task rather than a route to optimization. And similarly they’ve often been slow to react to evolving consumer needs. SoftPOS technology is gaining traction because it responds to both of these often-ignored growth opportunities.
How to protect SoftPOS apps
The benefits of SoftPOS technology are clear. Both for businesses and their customers. But as is the case with any financial trend moving digital, the dangers posed by hackers have to be considered.
So, how can we protect SoftPOS apps?
Well, as we’re fond of repeating here at Licel, the best way to make sure your app is safe for your end users is to design and develop it with security top of mind.
Take a look at our 7 security by design principles for an introduction after you’re done reading this article.
A key theme that runs through those 7 principles is empathy. A good place to start in keeping SoftPOS apps secure is to first put yourself in your customer’s shoes, and then imagine yourself as the hacker. This activity will help you to carry out a threat assessment, as the vulnerabilities of sensitive payment assets and security functions will become clearer to you.
As you might expect, the mobile payment sector is a highly regulated one. Typically these regulations are led by card payment system providers such as Visa and Mastercard. But there are also two standards that have to be met. One is set by EMVCO, and the other by PCI. Their security requirements are extensive and are a must read for any company looking to develop a payment app.
Put simply, the best way to adhere to these requirements is to use a multi-layered and dynamic security model. In other words, one where there’s no single point of failure.
But there are also specific areas that need to be covered.
The first of them is to do with code protection. Valuable code needs to be obfuscated so that hackers aren’t able to make any sense of it. That way they’re denied a base camp within the app from which to launch an attack. Cryptography can also be used to protect calls for sensitive logic.
Another key requirement involves the use of device attestation. This means being able to check that a device isn’t rooted, that it hasn’t been debugged, and that it isn't using an emulator, for example. It’s also there to make sure there are no attempts to hook sensitive methods and exfiltrate valuable data or key material.
These checks are crucial in the modern world as bad actors shift their focus to dynamic analysis - an easier and more efficient way for them to carry out an attack.
That’s why the app itself and the environment it’s operating in should also be constantly monitored for evolving threats.
And it’s important to be able to react to these threats, which is where risk analysis or threat intelligence systems come in.
As SoftPOS works with a real payment card, it’s also crucial to secure cryptographic storage for issuer keys. You need a self-defending model that can store cryptography keys securely and perform some cryptographic operations.
Both the EMVCO and PCI standards reference a virtual trusted execution environment (vTEE). A vTEE is vital for transfers to be processed securely without interference from hackers. In practise, this involves moving critical material to a secure, isolated container.
Is SoftPOS the future of payments?
At the beginning of this article we touched on the idea of major global events fast-tracking trends. Innovative inventions and businesses are often born out of a crisis because specific aspects of our lives - that we might have ignored before - are examined with a sharper focus.
This is how the sharing economy emerged from the last financial crisis, for example.
Companies like Airbnb and Uber are now so entrenched in everyday life that it feels like a trick of the mind that they’ve only been around for a decade or so.
And it's happening again as a result of the covid-19 pandemic.
The phone was already becoming a payment hub thanks to the normalization of challenger banks, mobile wallets, and even the influence of social media companies like WeChat in China.
That said, it was more of a tool for making payments than receiving them. SoftPOS enables the phone to be just as helpful for sellers as it is for buyers.
We can’t say for sure what the economic landscape will look like in the post-coronavirus world. But we have some clues. Businesses will become more mobile as city centers empty of workers. And more people are set to become freelance out of both choice and necessity. These people will need an easy and fast way to sell their products and services.
It’s hard to imagine a scenario where SoftPOS technology doesn’t thrive in this world. Particularly as the signs are that Apple will soon join Android in allowing users to take payments on their mobile, which will open up another huge section of the global market.
Think of it as just one more kick to fast-track the SoftPOS trend.