Mobile threats have evolved to target the entire channel - from the user, to the device, to the application, and the backend. In this edition, we explain how our product improvements are helping to ensure the integrity of each of these layers.
The mobile device ecosystem is probably the most diverse ecosystem in the IT world.
We’re not only talking about smartphones. Mobile and connected applications are running across smart sensors, TVs, home appliances, smart watches, tablets, and many other types of device. Hardware architectures vary, and so do operating systems and platform models - from Android and iOS to newer ecosystems such as HarmonyOS NEXT.
At Licel, when we think of protection we think in terms of the entire mobile channel: the multiple layers that connect with one another whenever we interact or transact in the digital world. In this latest edition of the Layers Bulletin, we’ll explain how our ongoing product updates are helping to make this channel stronger. The focus is on DexProtector - including its mobile API protection - and Alice Threat Intelligence, which plays a central role in our clients’ fraud-prevention strategy.


What's new with Licel's solutions?
Protecting the Whole Mobile Channel
As the mobile device ecosystem grows, so does the attack surface. Attackers are no longer focused only on the application package. They also target the backend, the communication channel between the two, device integrity, user sessions, and the telemetry that financial institutions and mobile payment providers use to make real-time decisions.
That’s why we believe organizations need to begin thinking about holistic mobile channel protection. In next month’s edition, we’ll share exactly what this looks like in practice and how it goes beyond traditional mobile application protection.
The increase in bot attacks targeting the backend systems of mobile applications is a particularly compelling case for mobile channel security. These attacks combine automation, reverse engineering, API abuse, device farms, emulators, and modified application flows, and no single defense addresses all of them.
If you’d like to better understand how to mitigate these attacks, read on to the end of this edition. We’ve written a deep-dive article that explains the anatomy of mobile API bot attacks and proposes a multi-layered defence plan.
With that in mind, we’ve decided to make DexProtector’s Mobile API Protection feature available to all DexProtector Enterprise customers from the next release. By connecting application protection, runtime integrity, network security, and device intelligence into a single mobile channel security model, it gives organizations grounds for greater backend confidence.
Android 4.4 Support
When we launched DexProtector 15 years ago, we offered support for Android 4.x. Since then, the mobile world has changed dramatically, and the latest DexProtector version supports modern Android releases, such as Android 17 QPR1, and iOS 26. Our goal hasn’t changed: to deliver the highest security standards in the industry for users of protected applications.
Based on device insights from Alice Threat Intelligence since November 2025, the number of Android 4.4 devices we still observe is now close to zero. Because of this, we’ll begin discontinuing Android 4.4 support in our mobile channel protection solution from November 2026.
If your users or business processes still depend on Android 4.4, please contact our support team at primary@licelus.com so we can discuss your requirements in advance.
Mobile Malware Detection: New Visibility for Alice Threat Intelligence Customers
Malware remains one of the main threat factors for mobile applications and devices, especially in banking, payments, and identity use cases. This risk is particularly important on Android, where users have more flexibility to install applications from different sources, including those that may be untrusted, poisoned, or controlled by attackers.
To help clients identify and mitigate these threats, our mobile channel protection solution includes Anti-Malware functionality. It can be used in monitoring mode or in active prevention mode, depending on the customer’s risk model and business requirements.
This threat is often underestimated, especially when organizations lack visibility into what’s actually happening on end users’ devices.
To address that, from the next DexProtector release, all Alice Threat Intelligence customers will automatically receive information about detected malware on their end users’ devices. Security and fraud prevention teams will gain clearer visibility into malware activity in the field, supporting faster incident response and a more accurate picture of the real threat posture across their mobile user base.
The Latest Alice Threat Intelligence Updates
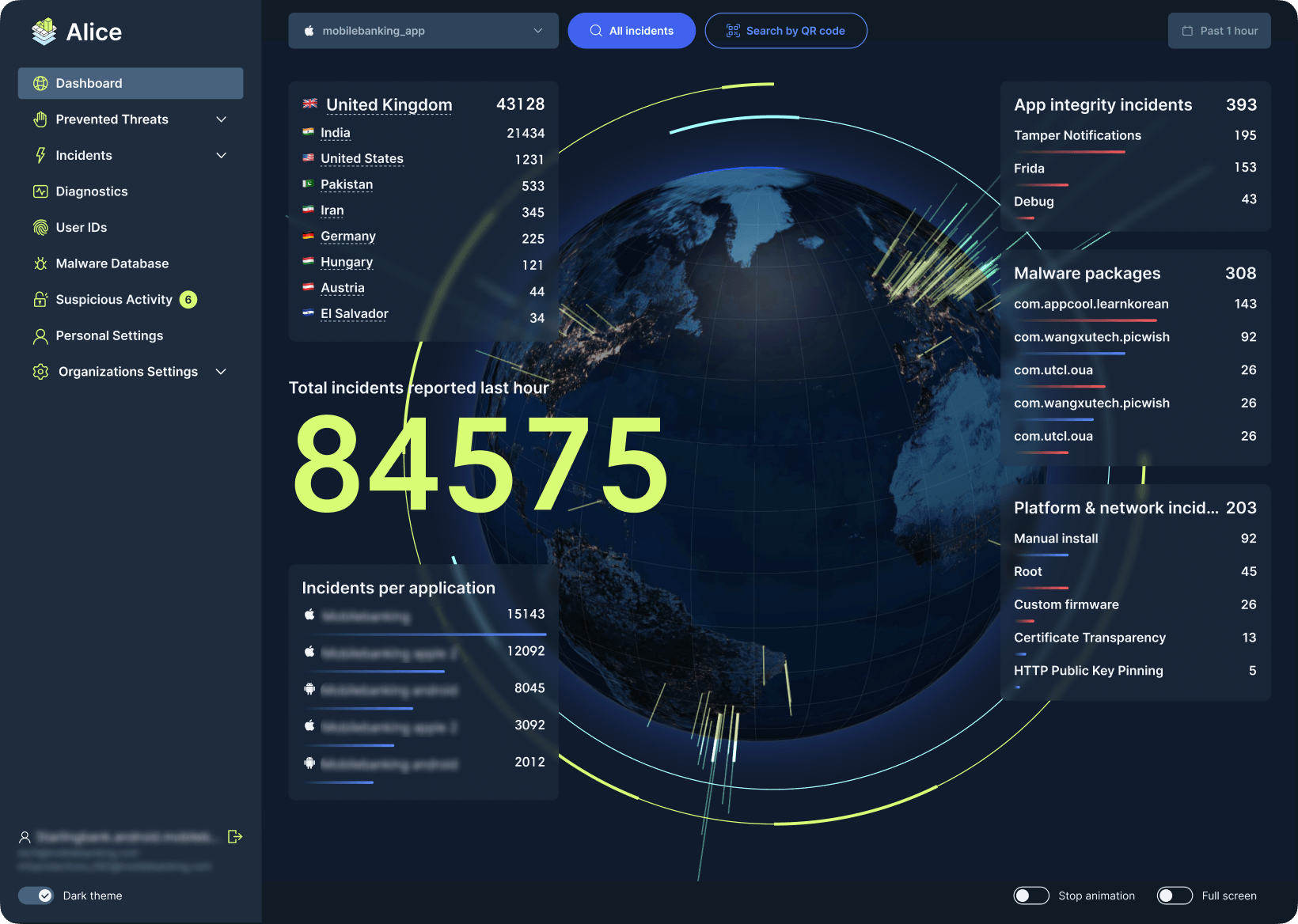
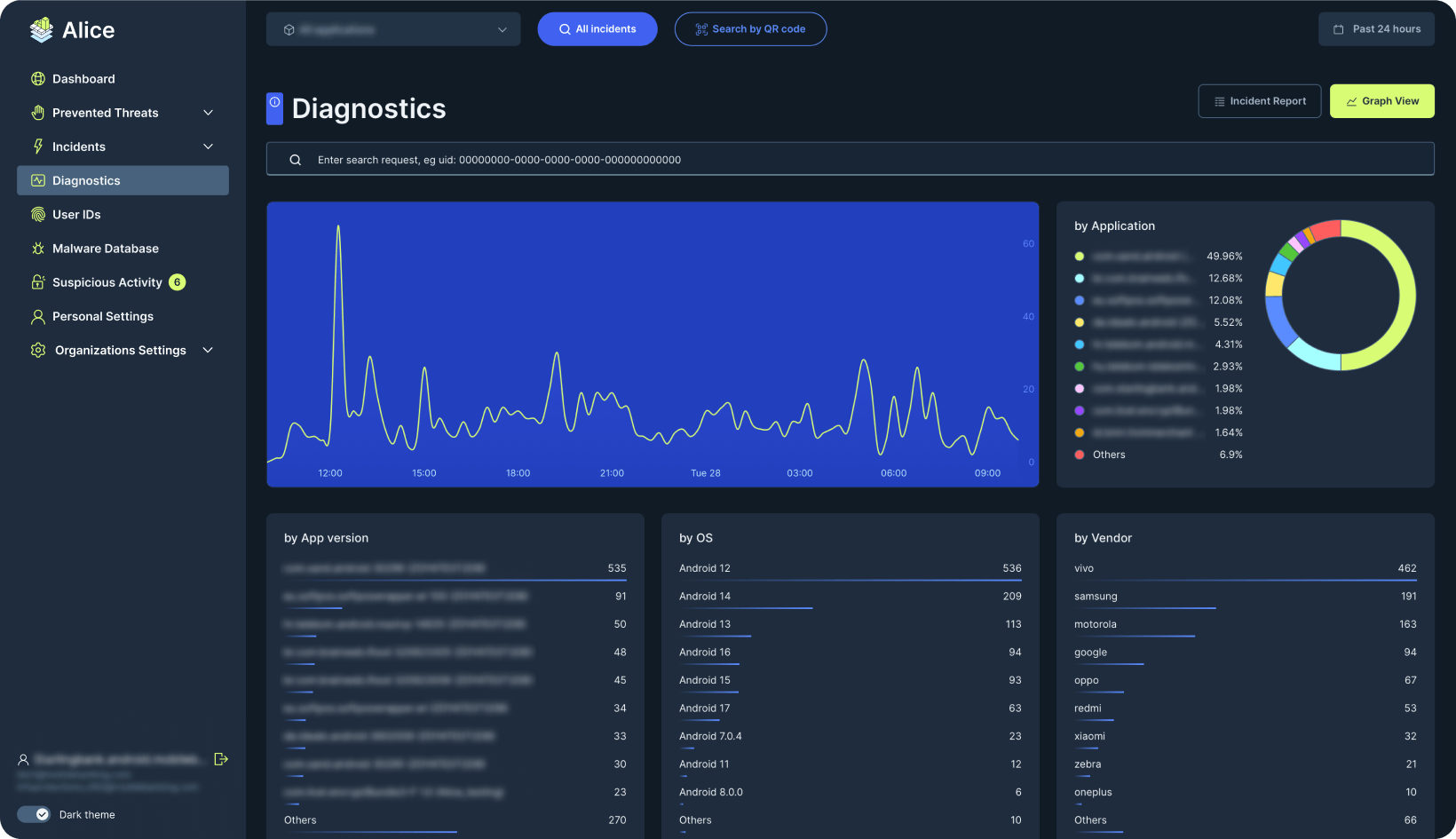
Alice Threat Intelligence supports a wide range of use cases, from SOC and incident response to compliance, audit, and real-time fraud prevention. The latest release introduces several improvements that help organizations better understand what is happening across their protected mobile applications.
These include:
- updates to the Alice interface to make investigation workflows faster
- new functionality in the Alice Globe view
- advanced classification of diagnostics information
- a new Subscriptions page with usage statistics, including for the Alice Enterprise API, giving teams clearer visibility and control over active subscriptions
Together, these changes help customers investigate incidents faster, and use trusted application-side signals as part of their fraud prevention and operational security workflows.
Mobile security is changing because the mobile ecosystem itself is changing. More devices, more operating systems, more application formats, more backend dependency, and more AI-driven automation means more sophisticated attacks and a new set of challenges for organizations that rely on mobile applications as a critical business channel.
Our goal with DexProtector, Alice Threat Intelligence, and the Licel vTEE, is to help customers protect this whole mobile channel: from the application package and runtime environment to backend confidence, malware visibility, and real-time threat intelligence.
Our team is available to help customers plan upgrades, review their protection configuration, or work through how these new capabilities apply to their environment.


Attack trends
Protecting Mobile APIs from Bot Attacks: Why Request Signing Alone is no Longer Enough
TikTok’s API request signing mechanism is often cited in reverse engineering communities as one of the more complex signing implementations in production. And yet it has been reverse engineered and circumvented by developers working in the open, and targeted by bot services. If the signing logic runs in the attacker’s environment, complexity buys time but not immunity.
Bot attacks targeting Mobile APIs are a clear example of the multi-layered, sophisticated threats organizations now need to guard against.
In our latest Knowledge Hub guide, we explain why mobile APIs should not blindly trust requests simply because they have been correctly signed, and why integrity verification is required to confirm the request itself was generated by a genuine, untampered app instance operating under acceptable runtime conditions.
This shift from signing to mobile trust enforcement mirrors the multi-layered mobile channel protection that we’ve recommended throughout this edition of the Layers Bulletin. It’s a shift that will likely separate organizations whose APIs remain easy targets from those whose APIs are not.
Thanks for reading this edition of the Licel Layers Bulletin. We'll be back next month with more product improvement updates and threat intelligence insights.





